Featured
Why investments in the biometrics sector can make an impact
The use of biometrics as an added layer of online security has increased in popularity but it still has flaws.

Is biometrics enough to protect our property, our money, our family, and our very lives?
Security and tech analysts are usually the first to say a cautious “yes” to this. The traditional use of passwords and other encrypted information has shown itself vulnerable to cyber attacks from hackers bent on stealing the user’s information. All it takes is an inventive mind, enough familiarity with the movements of the online space, and enough time for the cyber intruder to glean your security protocols, neutralize them and raid your treasure trove. If Yahoo!’s billions of emails have been compromised, and Google is regularly stepping up its firewalls and other protective virtual platforms, then no one is safe. Nor should anyone remain complacent.
Biometrics, however, has posed as a promising alternative because it uses elements of the human body and its physiologies as the protocols of a security system. In 1982’s Star Trek: The Wrath of Kahn, the computer scanning of his retina to verify his identity was considered ingenious. Today, it is run-of-the-mill. Nobody was awed or dumbfounded in The Avengers movie when the villain Loki dug out a hapless executive’s eye from its socket to enter his precious vault.
Aside from the visual cortex, fingerprint, voice and facial recognition are among the most used tools of biometrics. The confidence that many have placed in the field is understandable. While identifying a password or lifting it from a database is doable, it is impossible to totally fake another’s DNA, exact facial features, and a fingerprint mark. Loki’s eye theft, fortunately, remains within the purview of science-fiction.
Another advantage of using biometrics is that the user has zero risks of losing them. You might forget your password or even your security protocol, but you certainly can’t change your skin tone, eye flicker, or voice modulation.
Gulf News names two ways by which biometrics is being used by industries in everyday life, at least in the developed countries. Facial and voice recognition are regularly employed in airports and other public places to ferret out terrorists, criminals, and other wanted parties from the rest of the crowd. A suspect in disguise may be able to fool a human inspector, but facial recognition software may see him through his mask.
Another way by which biometrics is used is selfie banking. Banks regularly ask account holders to authenticate themselves during transactions. Often the methods resort to voice verifications with confidential data being asked for the phone. Biometrics will simply require the account holder to take his selfie on his camera and send it to the bank where software algorithm will compare his pictures to past profiles and greenlight his identity.

Biometrics has its ups and downs and just like any security protocol it cannot be 100 percent trusted. (Source)
According to Forbes, Apple Pay is elevating the practice a few steps higher. Instead of sending his credit card information over the phone to pay for a product, the user will just be asked to scan and send a biometric feature like a fingerprint or a facial mark.
Still, for all its attractions, biometrics has its limitations and challenges. One should not just employ them hastily and without preparation.
First, theft of biometrics is possible. Any hacker who has the tools and the know-how can crack any corporation database and steal the biometric data of its employees. This is not hypothetical; Wired reports that about the fingerprints of 6 million government workers were stolen from the U.S. Office of Personnel Management.
Second, as Dark Reading points out, this kind of theft opens up the users and account holders to other and possibly worse nightmares. To compare: stolen credit card information can force the poor user to pay for the thief’s online shopping. However, the theft of his fingerprint can land him in hotter waters, as the thief may use said fingerprint to create driver’s licenses, access social security benefits, or even fake medical conditions to get hospital benefits.
Third, biometrics has still to be proven 100 percent effective when it comes to detecting and curtailing violence such as acts of terrorism. Facial recognition may tip the hand of a disguised terrorist, but immediate intervention at the metal detector counter can lead to the shootout that the authorities are trying to prevent.
Biometrics is a viable option for protecting people and property from a theft of the cyber and physical kind. However, it also carries its share of risks and precautions must be in place as it is deployed. It might not yet be the great all-
encompassing answer to security, but it can come close.
(Featured image via DepositPhotos)

-
 Markets1 week ago
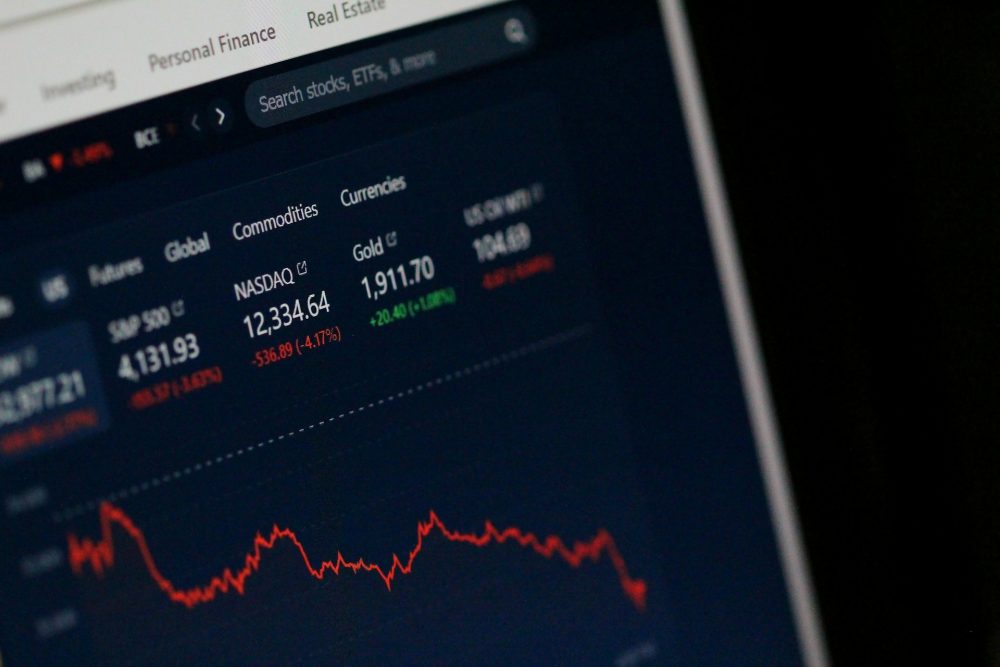
Markets1 week agoMarkets Surge Amid Rising Risks and Economic Strain
-

 Crypto2 days ago
Crypto2 days agoBitcoin and Ethereum Stabilize as Markets Watch ETF Flows and Institutional Moves
-
 Biotech1 week ago
Biotech1 week agoMolecular Health Insolvency Leads to Restructuring Under New Company Name Lucera GmbH
-

 Impact Investing2 weeks ago
Impact Investing2 weeks agoAlgebris Investments Backs CorPower Ocean to Scale Wave Energy Solutions















You must be logged in to post a comment Login