Business
5 things you need to know about the KRACK Wi-Fi vulnerability
Belgian researchers have exposed a vulnerability in the security of Wi-Fi connection called KRACK.
Recently, another cyber attack happened and it exposed vulnerabilities to Wi-Fi connections. Almost every device which connects to a Wi-Fi can be affected. Here are five things you need to know about it.
Patches can solve the problem
Experts suggest users patch their gadgets and devices now. Some companies have started offering patches (see below). Initially, companies could send emails to customers telling them to update as soon as possible. Patches are pieces of software that are released whenever a security flaw is revealed. Alternatively, if a customer has been able to identify a flaw, he or she can report the issue to the developers so they can develop patches.
Android 6.0 is affected the most
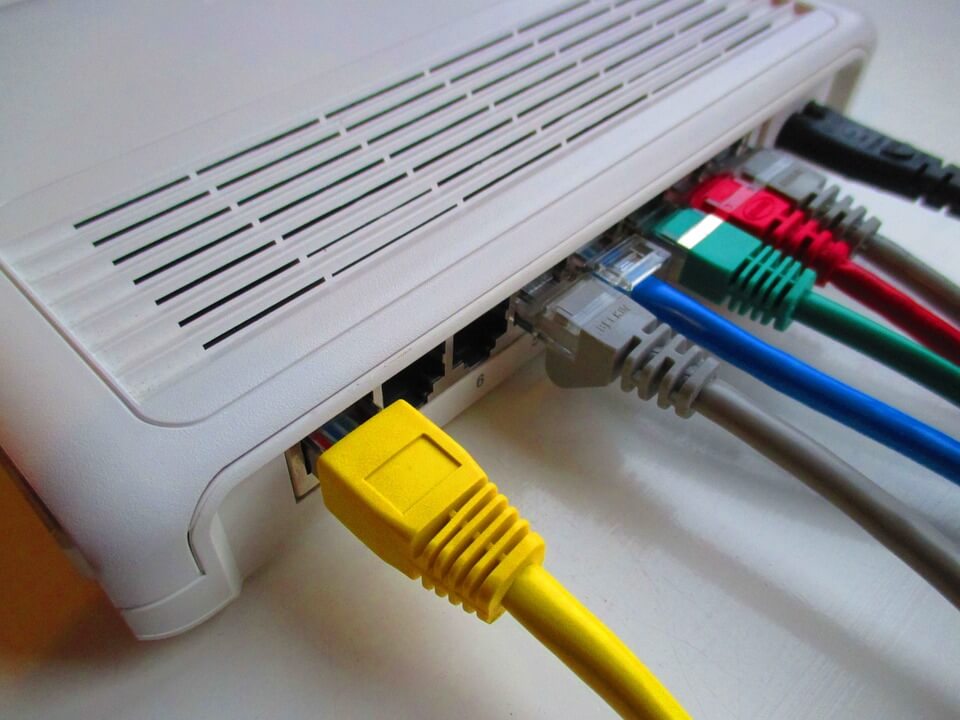
In essence, all devices that connect to the Wi-Fi can be affected. This means cars, wireless routers and home appliances in The Internet of Things are vulnerable. Ars Technica reported that Android 6.0, Chromium, and Android Wear 2.0 devices carry the fewest defense against a possible attack on the four-way cryptogenic handshake.
The four-way handshake is the industry standard when a user connects to a Wi-Fi. The process checks if the password is correct. Once verified, it deploys an encrypted connection between the device and the router. KRACK attacks this process, making devices vulnerable to ransomware or other malware from hackers.
KRACK means Key Reinstallation AttaCK
There has been no reported actual attack yet. What Belgian researchers Mathy Vanhoef and Frank Piessens of the Katholieke Universiteit Leuven have done is to expose vulnerabilities on the Wi-Fi Protected Access II (WPA2). WPA2 is responsible for encrypting traffic on Wi-Fi networks so that users can have a sort of protection from hackers and stalkers. However, WPA2 has been the industry standard since 2004, all Wi-Fi products have this feature making them vulnerable to cryptographic attacks.

Devices which have WPA2 are vulnerable to a KRACK attack. (Source)
Companies offering patches
Per Window Central, security companies have launched patches both for client and router can be found below:
- Apple
- Arch Linux: WPA Supplicant patch, Hostapd patch
- Aruba
- Cisco Meraki
- DD-WRT
- Debian/Ubuntu
- Eero
- Fortinet
- Intel
- LEDE/OpenWrt
- Microsoft
- MikroTik
- Netgear: WAC120, WAC505/WAC510, WAC720/730, WN604, WNAP210v2, WNAP320, WNDAP350, WNDAP620, WNDAP660, WND930
- Ubiquiti
- Raspberry Pi (Jessie, Stretch)
- Synology
- WatchGuard Cloud
Best defense is to disconnect
As they say, prevention is better than cure. For the meantime, Wi-Fi users are encouraged to refrain from connecting in public places. The experts also advised undergoing software updates.
WIRED noted that a hacker needs to be within the range of a Wi-Fi network physically to carry out the attack. It means that if an attack happens, it can be particularly limited in terms of victims at a particular time. However, as stated since WPA2 has been included in almost every device that is Wi-Fi ready, the scope of vulnerable appliances or gadgets is massive.
Meanwhile, the Wi-Fi Alliance said in a released statement that the group “now requires testing for this vulnerability within our global certification lab network and has provided a vulnerability detection tool for use by any Wi-Fi Alliance member.” This means, new devices produced from here on are protected while the old ones are not.

-

 Biotech6 days ago
Biotech6 days agoArgentina Expands Flu Vaccine Production Through PAHO Partnership
-

 Impact Investing2 weeks ago
Impact Investing2 weeks agoGreen Bonds Lead $241 Billion Sustainable Bond Market in Q1 2026 According to Moody’s Data
-

 Crypto3 days ago
Crypto3 days agoCardano in Decline as Hoskinson Distances Himself Amid Growing Uncertainty
-

 Cannabis1 week ago
Cannabis1 week agoHemp Boom to Bust: America’s Regulatory Reset and Europe’s Warning
























You must be logged in to post a comment Login