Business
Hackers to exploit Intel security flaws, experts warn
Security patches have been released by tech companies to combat the Spectre and Meltdown security flaws.

The tech industry was rocked recently after researchers discovered major flaws in computer processors which could affect up to billions of computers. The experts believe it will only be a matter of time before hackers could try to exploit these flaws.
According to CNN, the two flaws, called Spectre and Meltdown, pose serious concerns. The two have been existing for more than 20 years and it is believed computers and smartphones are affected by the bugs. Right now, the only safe thing to do is update security programs on mobile phones and computers.
The UK’s National Cyber Security Centre claims there have no known attacks, however, that does not mean it will not happen. The bug called Meltdown triggers laptops, desktop computers and internet servers using Intel and Qualcomm processors. On the other hand, Spectre has the potential of a bigger damage since it attacks processors made by Intel, ARM and AMD.
Patches for Intel security flaws
So far, security patches have been deployed to as added defense to Meltdown. Intel has tapped Apple and HP to distribute its firmware patches for its processors. Patches for Windows, Android, macOS, iOS, Chrome OS, and Linux are reportedly available as of the moment. Preparing for Spectre is not as simple as it seems.
Chrome, Firefox, and Edge/Internet Explorer are all vulnerable to Spectre and its patches may still require updating hardware for better protection in the long run. Amazon Web Services is also doing its own security patches. Google has already implemented Reptoline in its Google Cloud Platform.
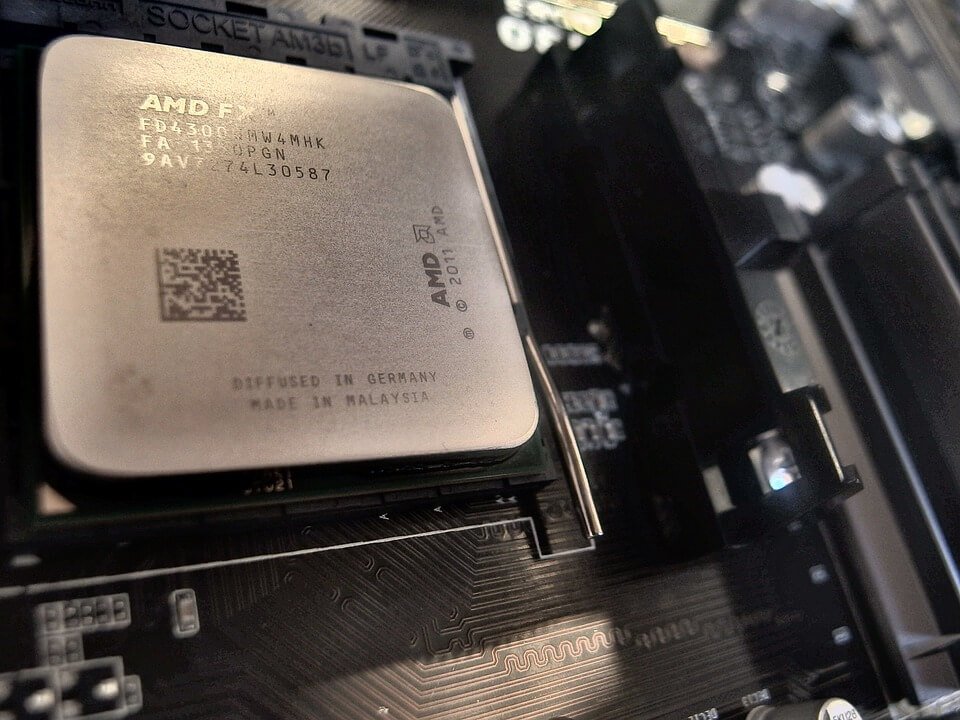
The industry rushes to safeguard against possible attacks through the Intel security flaws, named Meltdown and Spectre. (Source)
If the researchers who discovered the anomalies were to ask, the security flaws are downright scary. They Moritz Lipp, Daniel Gruss and Michael Schwarz from the Graz’s University of Technology tried to test one of their theories on how processors defend the most critical part of the computer memories. Gruss later found out he could extract personal information such as browsing history and email contents from the kernel, known as the most protected part of the computer’s operating system.
“You don’t expect your private conversations to come out of a program with no permissions at all to access that data,” Gruss added. After informing Intel of their discovery, the trio was told that they were not the ones who first discovered it. In fact, other experts have unearthed the flaws just months from one another.
Far-reaching consequences
Security researcher and Harvard Belfer Center fellow Bruce Schneier suggested that the multiple discoveries of Spectre and Meltdown teach everyone a lesson. “If the NSA discovered it, it’s likely some other intelligence agency likely discovered it, too—or at least more likely than random chance,” he believes.
The worst case scenario could be hackers stealing information such as passwords. The best way is to update security systems but experts reveal that people should expect that their computers will slow down by as much as 30 percent.
People would rather have slowed down computers than stay vulnerable to future attacks caused by security flaws that in all honesty, no one can gauge the number of damages it can possibly bring.

-

 Crypto1 week ago
Crypto1 week agoDeFi Hacks Surge in 2026, Exposing Major Security Weaknesses in the Crypto Industry
-

 Business2 days ago
Business2 days agoTopRanked.io Weekly Affiliate Digest: What’s Hot in Affiliate Marketing [+ The Best Affiliate Program Directory on the Internet]
-

 Crowdfunding6 days ago
Crowdfunding6 days agoSpain’s Crowdfunding Sector Surges as Real Estate and SME Financing Expand
-

 Biotech2 weeks ago
Biotech2 weeks agoFDA Approves First Treatment for Chronic Hepatitis Delta Virus (Hepcludex)























You must be logged in to post a comment Login